Applies to: Windows XP/2000/2003, Rohos Disk encryption software.

Summary: There are about a dozen of similar disk encryption programs (on-the-fly encryption and decryption). But the Rohos Disk offers an easier and more convenient way of working with the secret disk. The information is still well protected, but working with it is much easier. One step to create encrypted diskAfter the program has been installed, Rohos Wizard is analyzing the configuration of the computer and selecting the size of the disk and the other properties that will fit your system. All you need to do in order to start the Rohos disk encryption is just to set the disk access password and click “Finish”. At the same time you can change all disk properties, as well as set up the USB Flash drive for keeping the disk password.
The other programs lead the user through all possible settings, making them wonder what option to choose. It sometimes causes difficulties because there are no default value. You can’t just press “Next”.
You will unavoidably have to specify:
Main Disk for quick accessThe Main Disk can be quickly connected and disconnected by pressing one button. It is very easy and convenient. You should make minimal effort to start working with your secret files! All the similar programs let the user create several virtual encrypted disks Actually, it's convenient – you have 2 or 3 disks for different purposes. But in fact 90% of users of such programs create only one encrypted disk for storing their private files and folders and use only that disk. The interfaces of most similar programs are overloaded with extra features with the purpose that a user will create several virtual disks. As a result, the work with the program can involve difficulties, because the users always have to specify which disk they'd like to use, even if only one disk is in use. As a way out, user has to create tags for turning on the secret disk. The Rohos program is originally intended for working with only one disk. At the same time there is a possibility to create secondary disks. They can be connected by means of a shortcut or by specifying the path to the disk image. This option was created for advanced users. It allows the following:
Disk icon is in each application including MS Office!The similar programs assume that if you have a disk in the system you have an integration. The Rohos developers offer a new approach, using new features of Windows 2000/XP. The Rohos disk icon is now available from:
This makes the work with Rohos disks easier and more convenient. Program screenshots – disk creation, main window, dialogues…
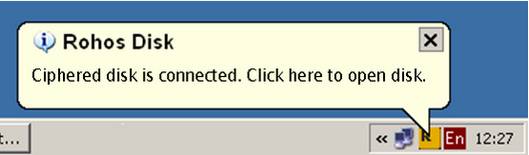
Turn on NotificationsWhen you turn on/ off the secret disk, you may see the notifications from Rohos in the clock area – they show that your personal disk appears in the system by your instructions, and becomes inaccessible (disappears) at the end of computer run.
You can also Open disk quickly by using the Rohos icon in the clock are, i.e. view disk contents in Explorer. For businessmen – automatic work of encrypted disk Now you have no need to turn on/ off the disk every time you want to open the document or the file of the disk. You just start working! It is possible if you use the program Rohos Logon Key which sets up a common Login for Windows and the secret disk (single sign-on). As a result, the user has enters the password once at the beginning of work. Rohos disk is turned on by your user account password in Windows. Built-in file-shredder Rohos disk contains a file-shredder which move your files and folders to your secret Rohos disk. After the movement the files are erased by the file-shredder and deleted. Additional Rohos disk services Now you may examine new Rohos versions and set up the update directly in the Rohos. The User Support dialog allows to contact directly to the program developers. You will receive reply via e-mail. More functions:
Links: Rohos - Data security program - entire disk encryption, steganography, file-shredder, access to the disk by USB Key. The password keeping on the USB flash drive - How to use USB flash drive as an access key to computer and personal data. Encrypted disk on the inside - What is a virtual disk? How do the encrypted virtual disk and 'encryption in passing' work? |
|