The new version of Rohos Disk (1.18) includes new utility, Rohos Disk Browser. This enables you to open and view the contents of secret partitions on a USB drive on any other computer, even if you do not have administrative rights.
The new version of Rohos Disk (1.18) includes new utility, Rohos Disk Browser. This enables you to open and view the contents of secret partitions on a USB drive on any other computer, even if you do not have administrative rights.
Rohos Disk can password-protect a portion of a USB flash drive, by creating a virtual encrypted partition. The partition is protected by a password, and can be opened on any computer. Now, even if you are in an internet cafe and have no administrative rights, you can still have read access to your secret partition with the help of the Rohos Disk Browser utility. This means that you can open any file and read any data. Naturally when you are at your home or office computer, you will still be able to work with your encrypted partition as usual.
On a strange computer you can always open your protected partition on the USB flash drive (in read-only mode) with the help of the Rohos Disk Browser utility. This makes it possible to open or copy only one particular file or directory, without granting access to every file.
This feature is enabled in a Rohos Mini Drive program – FREE and tiny USB drive encryption tool.

Read Rohos Disk Browser description...
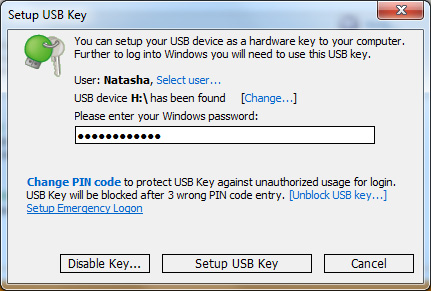
 Rohos Logon Key is the only software that allows to use USB flash drive as a 2-factor security key to access Windows Remote Desktop. It also supports Web Based remote desktop access with USB Key.
Rohos Logon Key is the only software that allows to use USB flash drive as a 2-factor security key to access Windows Remote Desktop. It also supports Web Based remote desktop access with USB Key.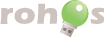


 Not long ago we bought APACER AH620 with 4 Gb capacity and fingerprint scanner. Embedded program allows to use password protected USB flash drive for data protection.
Not long ago we bought APACER AH620 with 4 Gb capacity and fingerprint scanner. Embedded program allows to use password protected USB flash drive for data protection.
 New device, 1 Gb MEM-Drive Biometric Scanline takeMS flash drive, came in our laboratory. Carry it Easy Plus Bio built-in program allows to use Biometric Authorization for data protection on USB drive. The present USB flash drive is compatible with
New device, 1 Gb MEM-Drive Biometric Scanline takeMS flash drive, came in our laboratory. Carry it Easy Plus Bio built-in program allows to use Biometric Authorization for data protection on USB drive. The present USB flash drive is compatible with
 The new version of Rohos Disk (1.18) includes new utility,
The new version of Rohos Disk (1.18) includes new utility,