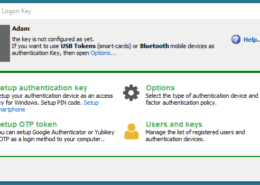
Two-factor authentication solution, allows you to protect any personal or corporate Windows login with easy-to-use multi-factor authentication. Built-in safeguards prevent 2FA / MFA bypass attacks. Allows protection with a wide variety of cutting-edge MFA methods like OTP, FIDO U2F tokens, Yubikey, smart-cards, RFID or smartphone push. Rohos integrates into conventional password-based Windows login and adds strong MFA control.
A fully functional 15-day trial
Your Computer security benefits:
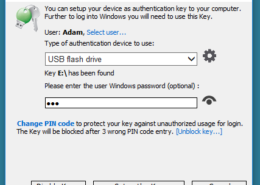
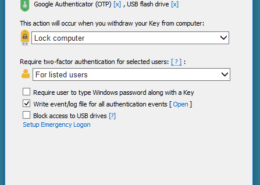
- Replaces weak password-based login with a hardware Security Key: USB flash drive, Google Authenticator OTP, FIDO U2F, Smartphope Push, Q/A login or industrial RFID access cards.
- Or adds two-factor authentication: Your Key + PIN code, or Key + Windows password;
- Uses a long and powerful Windows password, without the need to memorize it;
- Login with an electronic Key is fully automatic and fast!
- Authorize elevated operations in User Account Control request with a key as an easy click!
- The computer is password-protected, but you don’t need to enter it manually each time you log in, unlock/resume or authorize changes;
- Use a single key to log into your home, laptop and office computer;
- Have a few different MFA methods and devices for login into a single PC;
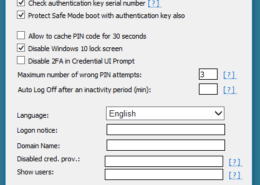
- Windows login is protected even in Safe Mode or Remote Desktop;
Employ a variety of authentication methods:
- Any regular USB flash drive or SD card;
- PKCS#11 security dongles like SafeNet iKey, eToken, Feitian token, etc;
- FIDO U2F security keys
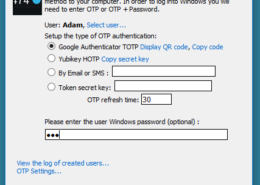
- Google Authenticator or YubiKey – OATH One-Time Password codes;
- Smartphone with Rohos push authenticator or Bluetooth ID;
- RFID access cards like MiFare 1K, Desfire, EM-Marine, Indala, HIDProx, smartcards;
- Compatible with Windows Hello devices
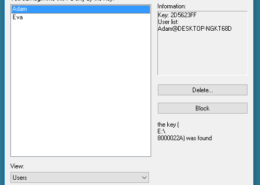
Rohos uses NIST-approved data-security principles and encryption: the password is not stored on the authentication key in open form. USB key copy protection prevents the creation of key copies without authorization. All data on the key is encrypted with AES-256 bit key length.
Authentication experience vs security:
Today many services offer strong two-factor authentication to protect your password-based access with additional electronic devices. While Rohos also provides you with complete usability in both, console or remote access cases:
- Use hardware security Key for console access and One Time Password generators like Google Auth/YubiKey/OATH for remote desktop access.
- An unlimited number of authentication methods can be configured for a single user account;
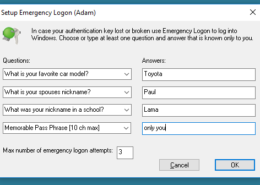
- Emergency Logon Q/A helps to log in to Windows if you’ve lost your key or forgotten the PIN code;
- For 2FA you can set a short PIN code to protect your key against “social engineers” around you. After 3 wrong PIN code attempts the Key gets locked for login;
- PIN Pad window has numeric buttons, keyboard entry and auto-focused field.
- Unprotected user accounts may be hidden from the Windows Logon screen.
If you work in an absolutely trusted environment, then you can use single-factor authentication mode that allows replacing your password with a digital Key.
Secure Active Directory authentication
Rohos Logon Key can also be used in your Windows enterprise network to secure authentication and save your budget:
- Install a domain-wide second-factor authentication requirement;
- Protect workstations and remote desktop;
- Second-factor variety: OATH OTP, Security keys, different models and brands, regular flash drives, RFID industry cards;
- Use any of One Time Password generators: Google Authenticator, SMS, by Email or physical OTP token;
- Offline and isolated workstation support, custom 2FA notices, automated 2FA enrollment by scripting and more…
- Cost-effective licensing: per workstation, one-time payment, free minor updates;
- Integrated safeguards to prevent 2FA / MFA bypass attacks with detailed audit log of MFA events compatible with any SIEM to create instant push notifications and desktop session lockout.
Compatibility:
 |
 |
 |
Windows 7/8/10/11, including the latest Windows Server OS.
Secure 2FA login for:
- Any Windows computer;
- Active Directory workstations;
- Windows Remote Desktop Learn more…
- Mac computer;
For Mac computers
For Windows networks
Our customers:
Consumers, Finance, Industry,
Education and Governments;
Download brochure:
Rohos Logon Key.pdf